Leave a Comment:
8 comments
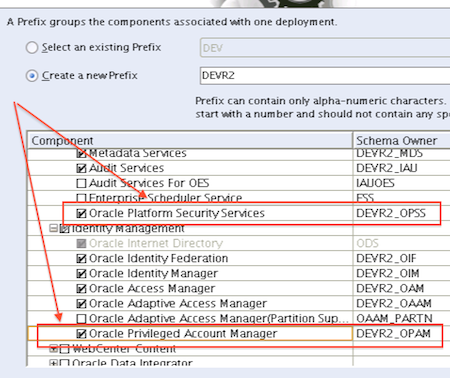
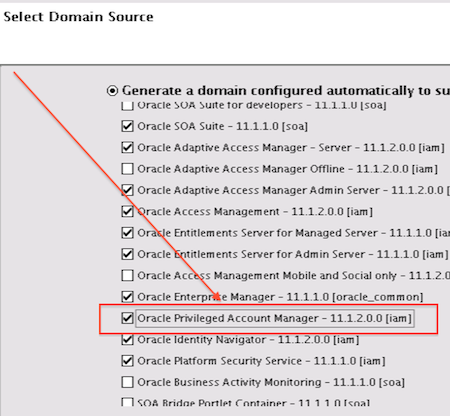
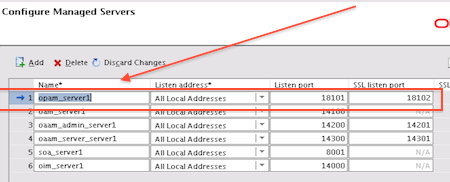
[…] Connectors 11. Events Handlers, Notifications, Reports, Scheduled tasks 12. Identity Analytics 13. Privilege Account Management 14. […]
ReplyWhen I run configureSecurityStore.py as part of OIM 11.1.2.1 install I get an SQLIntegrityConstraintViolationException: ORA-1: unique constraint (DEV_OPSS.IDX_JPS_RDN_PDN
This is recorded in oracle support under following bugnrs:
UNIQUE CONSTRAINT VIOLATION DURING DATABASE SECURITY STORE CREATION[Bug ID 16687761]
CONFIGURE DATABASE SECURITY STORE (CONFIGURESECURITYSTORE.PY) SCRIPT IS FAILING[Bug ID 16690836]
UPGRADE ERROR WHEN RUNNING THE CONFIGURESECURITYSTORE.PY SCRIPT TO CONFIGURE POL[Bug ID 16076126]
did you run into this and did you find a workaround?
greetz, Andre
ReplyHi
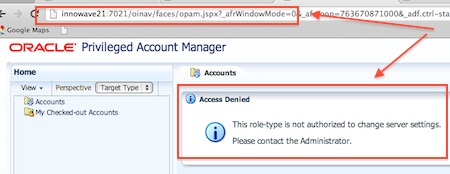
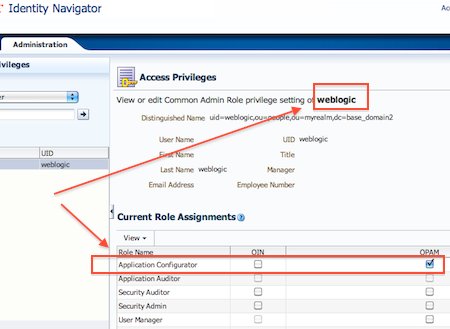
i have created a user in weblogic with which i am able to log in into opam console.
I have a added a Active Directory as a target and able to add 1 service account , Now when i am trying to grant this account to user which i have created in weblogic i am not able to find this user in search result
ReplyHi,
I am taking this exam very shortly .. Does anyone have any dumps for the same? or something that is going to help me clear the exam.
Thanks and Regards,
Sahana
I have installed OPAM. I have also added AD authenticator and i am able to see AD users as well as grant them accounts. My problem is that when a user logs in, he is not able to see the accounts i have granted him. What could be the issue here? Please help.
ReplyOPAM is used for providing passwords for privileged accounts at run time to the users.
My requirement is —-(can OPAM let applications use its password vault to connect privileged accounts.)
Ex. weblogic is connected to a data source using privileged account. can weblogic be configured with OPAM in such a way that weblogic has to use OPAM for password vault to connect to data source every time
ReplyHi,
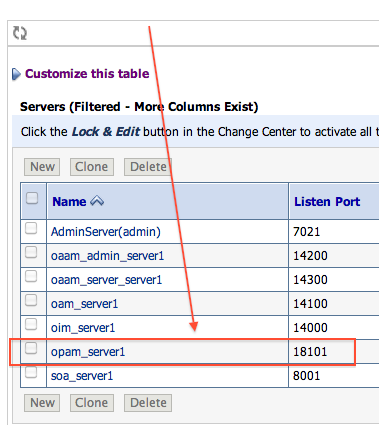
I have configured the OPAM. But when i hit the hostname:port/oinav/ URL it goes into loop and keeps on loading.. any idea?
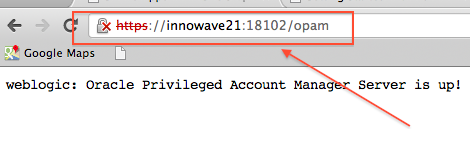
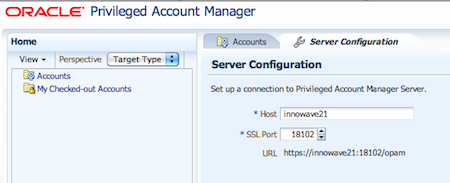
I installed OIM,OPAM in single domain. I am able to login into opam console but i didn’t get certificate with OPAM server URL. And still OIM,OPAM integration is required if we install in single domain?? please suggest me its urgent.
Reply