Leave a Comment:
17 comments
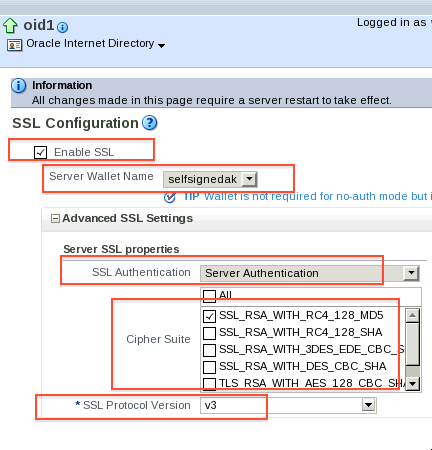
[…] SSL configuration in OVD – Oracle Virtual Directory Posted in January 27th, 2013 byAtul Kumar in idm, ovd, ssl This post covers key points and documentation to configure SSL in Oracle Virtual Directory (OVD) 11g. For SSL configuration in OID 11g click here […]
ReplyHi Atul,
Is there way to disable the nonssl port in OID? My requirement is to force all ldapbind with LDAPS port.
Regards,
Sunny
@Sunnyajmera,
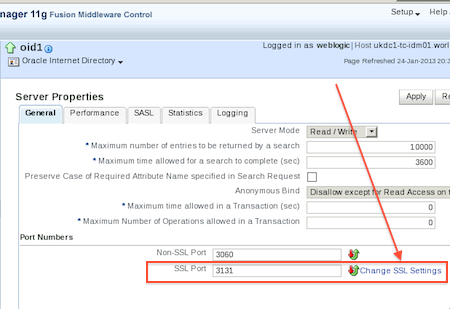
You can change LDAP port to LDAPS port. Use EM to change listener from NON-SSL to SSL , you can do same by changing LDAP attributes too.
[…] about SSL basics in WebLogic like Certifying Authority and Certificate and configuring SSL for OID and SSL for OVD using Graphical User Interface (GUI) like Fusion Middleware Control […]
Reply[…] recently configured LDAP Adapter in OVD (acting as proxy in front of OID) where OID is listening on SSL. This configuration worked and user’s were able to access OID data via OVD using LDAP […]
Reply[…] OID/OVD is configured to listen on SSL (for steps on how to configure OID/OVD in SSL click here and here ) then you select checkbox SSL Enabled in Provider Specific […]
ReplyHi Atul,
I have configured SSL on OID server as per steps mention in blog and i am able to connect to LDAP server using SSL port from ODSM application and able to configure SSL connection in OAM Data Source.
But how can we test it using any LDAP browser or web based application?
Any suggestion will be helpful and appreciated.
Regards,
Ashutosh
@ Ashutosh,
You download LDAP Browser like Apache LDAP client and then when you are connecting to OID select SSL and give SSL listener port of OID .
Thanks Atul for your reply.
I tried using Apache LDAP browser and jexplorer both and unable to connect.
Steps followed to configure SSL.
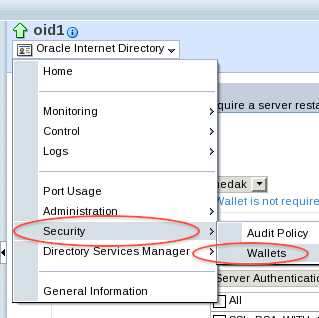
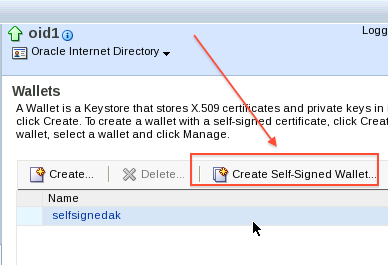
1. Created Wallet with auto login.
2. Added a Self-Signed Certificate in to wallet.
3. Configure SSL parameter using wlst. But i have not configured “NO Authentication” in SSL configuration.
4. At last, restarted OID instance.
Let me know, if missing any steps and does LDAP browser required any SSL certificate to connect to server?
ReplyThis looks good, when apache browser hit LDAPS on OID and if certificate on OID server are not in trust store of Apache LDAP , Apache is going to prompt to verify and accept certificate .
If you are not going till that stage, this means
a) Either firewall between client or OID
b) or Issue in OID SSL listener
Check OID access logs to see if request is coming to OID or not .
ReplyHi Atul,
I tried disabling firewall on IDM server and now while trying to connect using Apache LDAP browser after passing login information and selecting Simple Authentication, getting following error ”
The authentication failed
– The response queue has been emptied, no response was found.
org.apache.directory.api.ldap.model.exception.LdapException: The response queue has been emptied, no response was found.
at org.apache.directory.ldap.client.api.LdapNetworkConnection.bind(LdapNetworkConnection.java:1117)
at org.apache.directory.studio.connection.core.io.api.DirectoryApiConnectionWrapper$2.run(DirectoryApiConnectionWrapper.java:368)
at org.apache.directory.studio.connection.core.io.api.DirectoryApiConnectionWrapper.runAndMonitor(DirectoryApiConnectionWrapper.java:1175)
at org.apache.directory.studio.connection.core.io.api.DirectoryApiConnectionWrapper.doBind(DirectoryApiConnectionWrapper.java:460)
at org.apache.directory.studio.connection.core.io.api.DirectoryApiConnectionWrapper.bind(DirectoryApiConnectionWrapper.java:306)
at org.apache.directory.studio.connection.core.jobs.CheckBindRunnable.run(CheckBindRunnable.java:79)
at org.apache.directory.studio.connection.ui.RunnableContextRunner$1.run(RunnableContextRunner.java:122)
at org.eclipse.jface.operation.ModalContext$ModalContextThread.run(ModalContext.java:121)
Caused by: org.apache.directory.api.ldap.model.exception.LdapException: TimeOut occurred
at org.apache.directory.ldap.client.api.LdapNetworkConnection.bind(LdapNetworkConnection.java:1089)
… 7 more
The response queue has been emptied, no response was found.
“.
Tried looking on OID access log, i am not seeing any connection request.
Please advise.
Thanks,
Ashutosh
Thanks Atul for guiding me.
Issue resolved, it was due to wrong jdk version. Apache LDAP browser was unable to connect.
Later able to connect using some other browser (jexplorer) with jdk 1.7.x.
Another Question – Is it possible to generate or export certificate from wallet (configured SSL on OID with self sign certificate) for any web based application? If yes, then How.
Reply@Ashutosh,
You can copy whole wallet to another location and use it . Just copy and paste
Hi Atul,
it’s really a usable post,we are trying to enable SSL every where for my OBIEE setup which uses LDAP for authentication I followed all the above steps which you listed in this article but when I am trying to perform reassociatation of policy store from my OBIEE it’s error out with message like no trusted certificate found I can I open wallet and see what are all certificates are present in that ,how can I debug this.
thanks in advance .
Satish K.
Reply@Satish,
Do you see trusted certificates on trust store of client ?
Hi Autl,
it’s a lengthy query please bare with me.
Thanks for your quick reply ,here is what my current requirement is and what I followed in-order to make SSL every where .
My WLS uses LDAP for Authentication/Authorization so as a part of SSL every where in LDAP/WLS level I followed below set of instructions.
Related to certificate I have below files
1.trust.jks
2.identity.jks
3.root.cert
4.ewallet.p12
5.cwallet.sso
6.cacerts
LDAP Level SSL:
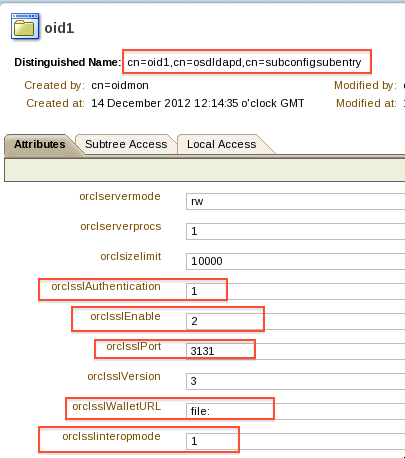
I placed my ewallet.p12 & cwallet.sso in some xyz directory and for “orclsslWalletURL” I provided that directory path and orclSSLAuthentication value as 32 even my db is SSL enabled so I modified sqlnet.ora and tnsnames.ora file accordingly post modifing all these changes I restarted all opmn components every thing looks fine upto this level.
WLS Console:
Under “keystores” tab Keystore type change to “Custom Identity and Custom Trust” and provided custom Identity/Trust Keystore file location and private key alias under “SSL” tab
WLS EM:
For Business Intelligence coreapplication component under Secure Socket Layer tab I provided CA certificate location and restarted all the services including Node manager.
Apart from above changes I replaced old certs file of jdk which wls server is using with the one I have in hand.
at the time of installation of WLS it’s plain env so ldap protocol and port numbers are ldap/3060 ,in-order to change those value from plain to SSL in weblogic I find a script of reassociation when I am attempting to run that script it error out with a message
Starting policy store reassociation.
Command FAILED, Reason: javax.naming.CommunicationException: simple bind failed: xyz.domain.com:3131 Root exception is javax.net.ssl.SSLKeyException: [Security:090477]Certificate chain received from yzx.domain.com – 10.147.45.97 was not trusted causing SSL handshake failure.
Certificate related file which I listed above have below conent
For some reasons I am just hiding the dtls and replacing with xyz
1.identity.jks
keytool -list -v -keystore identity.jks -storepass xyz
Keystore type: JKS
Keystore provider: SUN
Your keystore contains 1 entry
Alias name: xyz
Creation date: Mar 17, 2015
Entry type: PrivateKeyEntry
Certificate chain length: 1
Certificate[1]:
Owner: CN=xyz, OU=xyz, O=xyz, L=xyz, ST=xyz, C=xyz
Issuer: CN=xyz, OU=xyz, O=xyz, L=xyz, ST=xyz, C=xyz
Serial number: xyz
Valid from: Tue Mar 17 21:57:39 IST 2015 until: Tue Dec 11 21:57:39 IST 2018
Certificate fingerprints:
MD5: xyz
SHA1: xyz
SHA256: xyz
Signature algorithm name: SHA1withRSA
Version: 3
2.trust.jks
keytool -list -v -keystore trust.jks -storepass xyz
Keystore type: JKS
Keystore provider: SUN
Your keystore contains 2 entries
Alias name: xyz
Creation date: Mar 17, 2015
Entry type: trustedCertEntry
Owner: CN=xyz, OU=xyz, O=xyz, L=xyz, ST=xyz, C=xyz
Issuer: CN=xyz, OU=xyz, O=xyz, L=xyz, ST=xyz, C=xyz
Serial number: xyz
Valid from: Tue Mar 17 21:57:39 IST 2015 until: Tue Dec 11 21:57:39 IST 2018
Certificate fingerprints:
Signature algorithm name: SHA1withRSA
Version: 3
Alias name: mykey
Creation date: Apr 10, 2015
Entry type: trustedCertEntry
Owner: CN=xyz, OU=xyz, O=xyz, C=xyz, EMAILADDRESS=xyz
Issuer: CN=xyz, OU=xyz, O=xyz, C=xyz, EMAILADDRESS=xyz
Serial number: xyz
Valid from: Mon Aug 31 21:07:13 IST 2009 until: Sun Mar 26 01:02:21 IST 2034
Certificate fingerprints:
xyz
SHA256: xyz
Signature algorithm name: SHA1withRSA
Version: 3
Extensions:
xyz
3.cacerts
4.ewallet.p12
when I try to open this file using below command it’s telling it has 0 entries ,that’s the culprit causes this issue,if how can I populate this file using above files which I have along with me.
keytool -list -storetype pkcs12 -keystore ewallet.p12 -storepass xyz
Keystore type: PKCS12
Keystore provider: SunJSSE
Your keystore contains 0 entries
how can debug and fix this issue .
thanks again.
Satish K.
Reply