Leave a Comment:
17 comments
hi
in my project i am using IDM 11g(11.1.1.3.0) i had instilled the exchange and AD connector 9.1.1.7.0. but in my case AD is provisioning properly. where exchange is not provisioning resource it is giving the error (create mailbox is rejected) and i had installed the remote manager in the exchange server system
please help me in this issue
Reply[…] SSL in WebLogic Server – Part II : Create KeyStore, generate CSR, Import CERT and configure KeyStore with WebLogic Posted in February 10th, 2013 byAtul Kumar in ssl, weblogic This is part II of SSL in WebLogic Server that covers creating KeyStore, generating Certificate Signing Request (CSR), importing Certificate in KeyStore, and finally using this keyStore with WebLogic Server. I strongly recommend to go through Part I “SSL in WebLogic KeyStore, Identity & Trust Store, Root and Intermediate CA“ […]
Reply[…] newsletter edition we have published many new technical WebLogic articles like WLST Examples or SSL in WebLogic by Atul Kumar or Troubleshooting Tools by Laurent Goldsztejn. If you also write articles, Please […]
ReplyHi
i am new to the Weblogic, confused on importing the cert process, i followed the below,
Imported the certs in identity.jks in the below sequence
rootCa.cer
Intermediary.cer
Certificate.cer
my question, which of these files need to be imported in the Trust.jks file and in what sequence
@ Zia,
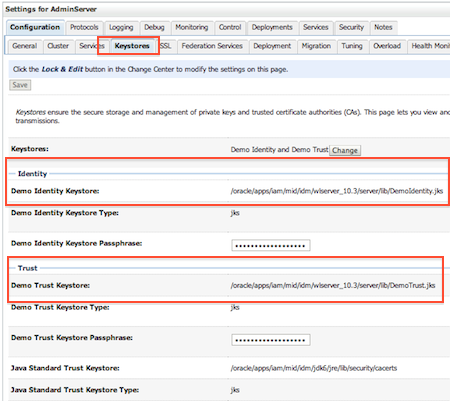
rootCa.cer & Intermediary.cer are Trusted Certs and are stored in Trust Store where as Certificate.cer is Idnetity Certs and is stored in Identity Store.
Having said that both Identity store and trust store can be stored in same file or in two different files (If same file then in weblogic give path to same file and if different then give different file location for Trust and Identity Store)
Still confused ??
Reply@ ZIa,
Please paste error you are hitting here and also command used to import signed certificate in to identity store .
[…] Posted in August 8th, 2013 byAtul Kumar in troubleshooting, weblogic I discussed about SSL basics and SSL configuration in WebLogic Server. In this post I am going to cover an issue encountered […]
ReplyHey Atul,
i ran the below commands to import the certs, and i was able to over come the issue with the Application related to scheduling the Flowcharts, the way i imported the certs is different, but it just worked for me.
Identity store
——————-
keytool -importcert -alias root -keystore Identity.jks -file primary_inter.cer
keytool -importcert -alias intermediate -keystore Identity.jks -file secondary_inter.cer
keytool -import -alias Alias-name -keystore Identity.jks -trustcacerts -file server.cer
Trust Store
—————-
keytool -import -alias Alias-name -keystore Trust.jks -trustcacerts -file server.cer
any advice on this Procedure
Thanks
Reply[…] line ?? ORAPKI Posted in August 24th, 2013 byAtul Kumar in oid, ssl I discussed about SSL basics in WebLogic like Certifying Authority and Certificate and configuring SSL for OID using Graphical User Interface (GUI) like Fusion Middleware Control […]
Reply[…] To more about SSL and steps to import CA’s certificate in WebLogic’s Trust Store click here […]
Reply[…] This is part II of SSL in WebLogic Server that covers creating KeyStore, generating Certificate Signing Request (CSR), importing Certificate in KeyStore, and finally using this keyStore with WebLogic Server. I strongly recommend to go through Part I “SSL in WebLogic KeyStore, Identity & Trust Store, Root and Intermediate CA“ […]
Replyhi,
javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: No trusted certificate found
can anybody help to fix it up
Reply@Ajay, In which component you are getting this error ? This means certificate of Certifying Authority is missing on client side. You need to import root and intermediate (if any) certificates in client trust store . Explain setup and place where you are hitting this issue .
ReplyHi Atul,
I have SOAP API based web service standalone application which will set challenge questions and answers for OAAM users. When I am connecting with http url from my standalone application it is working fine. When the moment I started using OAAM https url to fetch Bharsoa session from OAAM I am getting exception as “Exception Occurred while Reading license file”. So I added webserviceclient+ssl.jar file and changed the configuration of http handler to sun as “-DUseSunHttpHandler=true and -Dssl.debug=true” as oracle support suggested. After that I started getting exception as “BAD Certificate Recieved.”
Could you please suggest me anything on this?
Thanks in Advance,
Gupta Katakam
hi…I have learnt WebLogic Administration,Iam in searching of job on weblogic itself.So is there efficient demand for weblogic right now?I want to know please send your reply.thank you.
Reply