This post covers step by step instruction to configure OEM 12c (Cloud Control) so that it can monitor Oracle Identity Management component (OID/OVD). For overview of OEM Cloud Control 12c installation click here and to install OEM 12c cloud control using SIMPLE (You can use SIMPLE or ADVANCED mode to install) click here
Configure OEM 12c to monitor Oracle Identity Management (OID/OVD) 11g
1. Install OEM 12c Server
2. Install OEM 12c Agent on all machines hosting Identity Management (If Identity Management is deployed on multiple servers, more here and here then install OEM Agent on all machines)
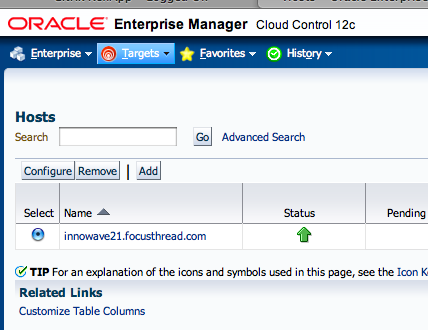
3. Verify that Host (where OID/OVD is deployed) is available in OEM 12c Cloud Console. Targets -> Hosts
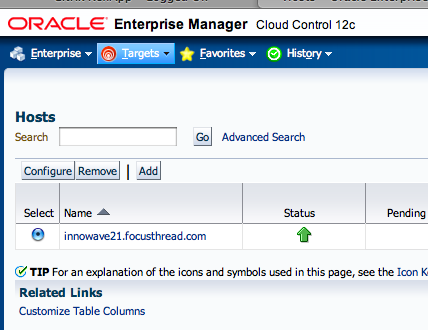
Note: In my case OID/OVD is running on host innowave21.focusthread/OEM 12c Agent
4. Ensure that OEM 12c server can talk to WebLogic Admin Server (Admin Server LISTEN port should be allowed to connect from OMS Server) that is managing OID/OVD (FMW EM running on WebLogic Admin Server manages OID/OVD components)
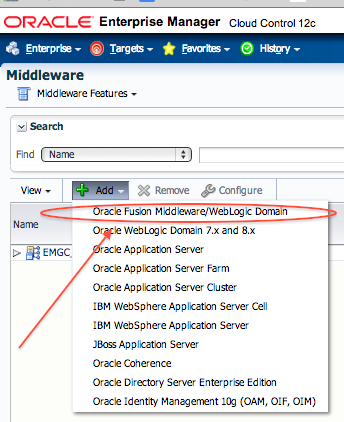
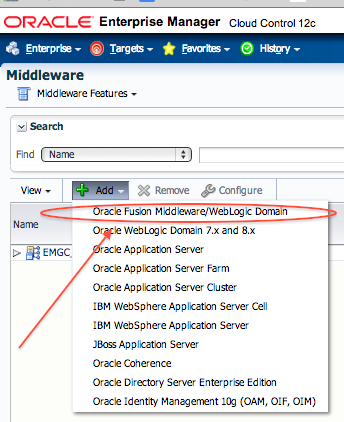
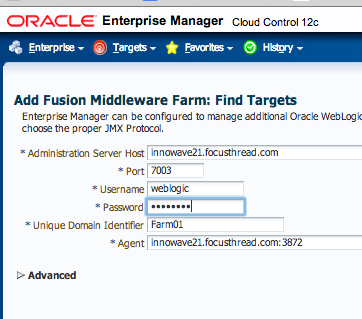
5. Add Middleware Target (WebLogic Server managing OID/OVD where EM is running): Targets -> Middleware -> Add -> Oracle Fusion Middleware /WebLogic Domain.
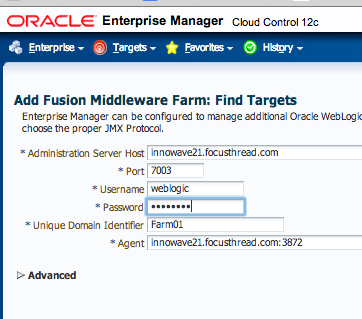
6. Provide Details of WebLogic Admin Server that is managing OID/OVD and click Continue . (If OID/OVD is not currently managed by any WebLogic Server then you can integrate it with WebLogic Server using opmnctl registerinstance )
7. You should see confirmation message that Finding Targets completed Successfully . Click Close on confirmation pop up window

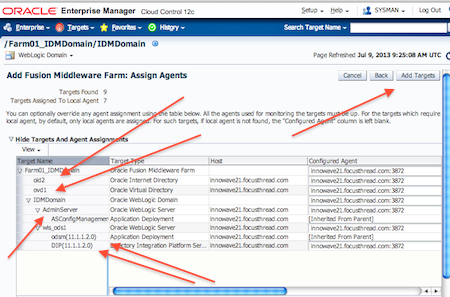
8. Verify that you can see all targets (OID/OVD/Admin Server, DIP, ODSM) that are moniotored by WebLogic Server and click on Add Targets
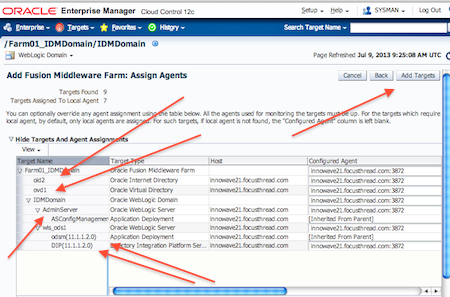
9. You should see confirmation message that Targets added successfully

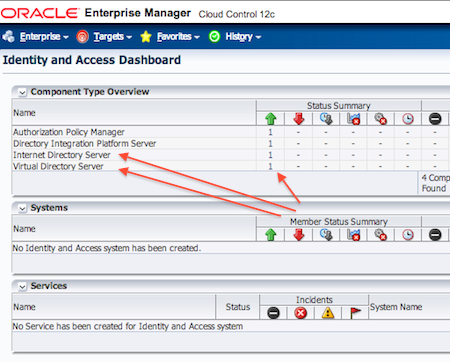
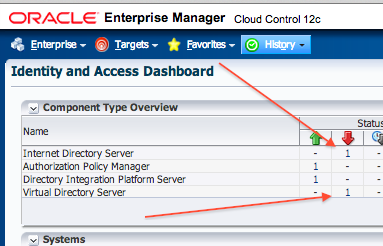
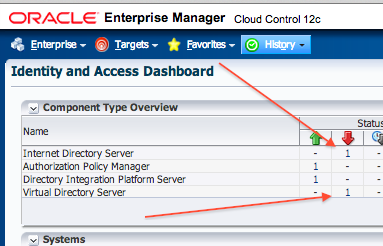
10. Check the status on Identity & Access Management Dashboard page : Targets -> Middleware -> Middleware Features -> Identity and Access
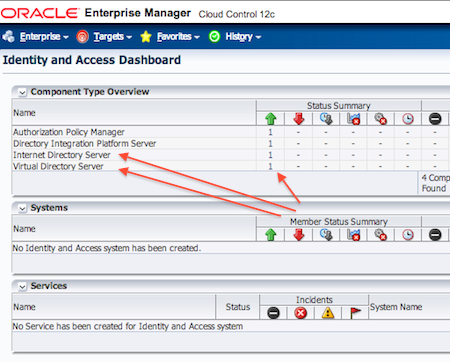
11. Test that on stopping OID/OVD services status for these components is shown as Down (Metric Collection for Service Status UP/DOWN is 5 minutes for OID and 1 minute for OVD which is configuration option)
12. Optionally you can configure Email Notification in OEM 12c Server and Create Incident Rules to send eMail notification for OID/OVD Service Staus to notify users via eMail. From OEM 12c onwards, Service Up and Down events (OID/OVD availability) are grouped in to Incidents and any action on incident is done via Incident Rules. Configure your Account in OEM 12c to “Subscribe to receive emails for Incident Rules” OEM CC -> Setup -> Incidents -> Incident Rules
13. You can also optionally configure SNMP traps
Configuring Beacon, Services and Service Level Agreement (SLA) to monitor OID/OVD/LDAP using OEM 12c in following post