This post covers topic 6 of certification 1Z1-459 Oracle Identity Governance Suite 11g Essentials i.e. Security
Topic 6 Security of certification 1Z1-459 contains following sub topics
6.1 Describe features of OES and how OIG leverages OES to create the security model
6.2 Configure a Delegated Administration model
1. Authentication : is the process of proving, you are who you say you are. Common method for Authentication in OIM are using username/password
2. Authorization : defines permission or access rights assigned to a user. Authorization defines what a user can see/do in OIM.
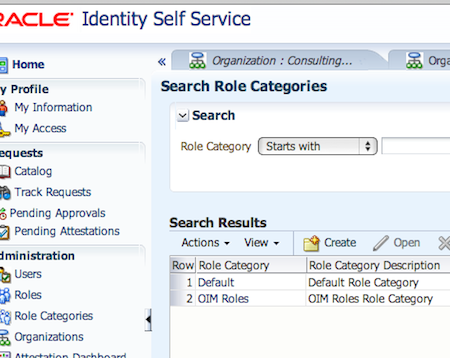
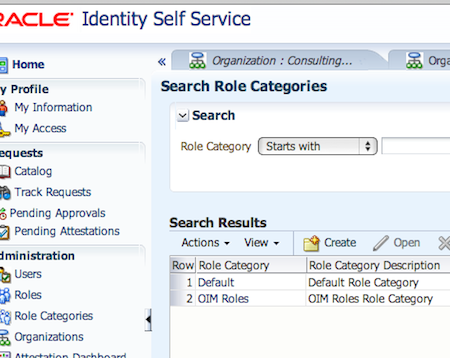
3. Role : Role are used to manage collection of users to whom you wish to permit same access rights or functionality. Role has a Category (collection of related roles in one category). By default there are two role category
a) OIM Roles: All pre-defined roles in OIM are part of OIM Roles category
b) Default: This is the default Role Category, If during Role creation you don’t specify role category then category default is assigned to Role.
4. OIM has authorisation engine, Oracle Entitlement Server (OES) embedded, that with help of authorisation policies in OIM controls what actions user can perform in OIM.
Note: Oracle Entitlement Server (OES) is used to define the authorisation policies that controls the access rights users have.
5. Authorization Policy : determine at runtime whether or not a particular action is allowed. Policies for OIM in 11gR2 version is defined in OES
6. Authorization Policy in OIM 11gR2 are managed by OES Admin Console ( http://weblogic_host:admin_port/apm )
7. There are three types of Administrative Roles in OIM like
a) Administrator : This role manages entire life cycle of the entity
b) Viewer : can see entity and request access for entity . If the viewer request entity then approval is required for viewer to view request
c) Authorizer : can see entity and request access for entity . If the viewer request entity then approval is NOT required for viewer to view request (authorizer get access directly)
8. Admin Roles that are assigned to Authorization Policy can be Global or Scoped
a) Global : These roles can only be assigned at root of organisation (top organisation) and applicable to entire OIM system, example of global roles are System Administrator, Catalog Administrator, System Configurator etc
b) Scoped : These roles can be assigned to top Organization or any other organisation that is under top Organization.
Further Reading