In Today’s post I am going to cover Identity Management related configuration used during Fusion Application Installation.
Contact Us If you are looking for Identity & Access Management or Fusion Applications Installation, Implementation or Training.
If you are not familiar with
OIM &
OAM then check my book on
OAM/OIM 11g available on
Amazon .
OAM 11g is used to
login to Fusion Applications where as
OIM 11g is used for
User/Password management &
Provisioning accounts to Fusion Applications. Check
Brian Eidelman’s post Identity Management components used in Fusion Applications.
1. Pre-requisite for Fusion Applications is to install, configure and integrate OID/OIM/OAM. When you integrate OIM/OAM using idmConfigTool, this tool creates properties file called idmDomainConfig.param
2. During Fusion Application Provisioning, you can use idmDomainConfig.param which will populate most Identity & Access Management screens automatically during Fusion Applications Installation.
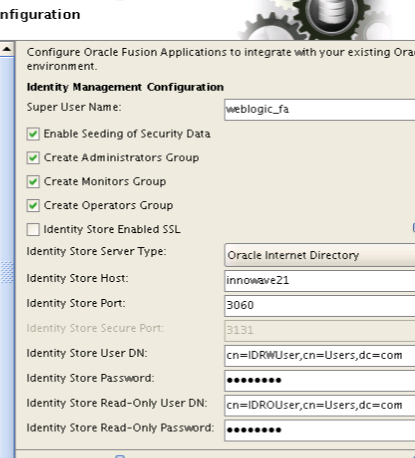
3. For Identity Management Configuration screen (during Fusion Applications installation), enter following :
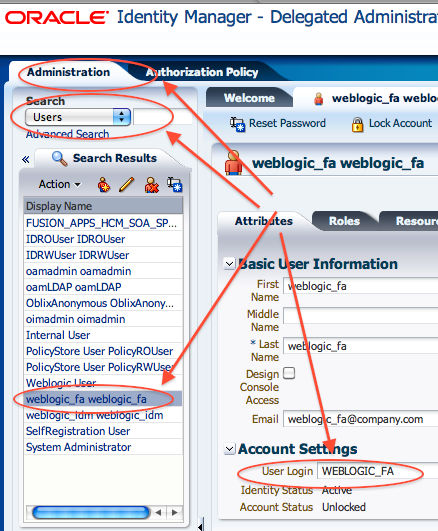
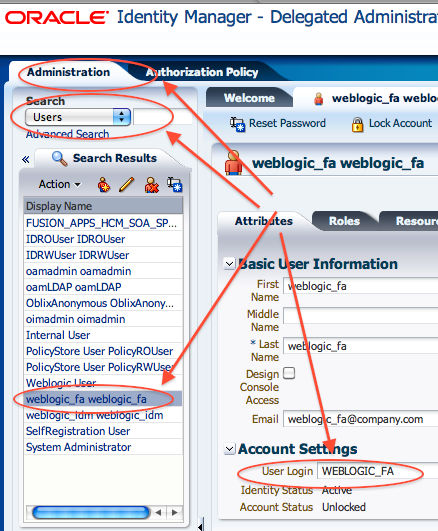
a) Super User Name: weblogic_fa (This is the user created during idmConfigTool.sh -preConfigIDStore more on idmConfigTool here ) : Make sure that you can see this user in both OID (via ODSM ) and OIM (manage user screen in OIM Administration Console). If User is missing in OIM then run Recon Jobs to bring users from OID to OIM (LDAP User Create and Update Full Reconciliation)
Note: During FA provisioning this user will be granted Administrator and Functional Setup privileges. You should use this user to login to Fusion Apps after installation.
- weblogic_fa user in OID (via ODSM ) :

- weblogic_fa user in OIM (via OIM Administration console):
b) If you have already created groups in OID related to Administrator, Monitors, Operators role then you can uncheck box next to them. If these groups are not created in OID then select checkbox for Enable Seeding of Security Data, Create Administrators Group, Create Monitors Group, Create Operators Group
c) OID by default listens on SSL (3131) and non-SSL (3060) port for any LDAP request. If you want to Fusion Apps to connect to OID on LDAPS (SSL) then select checkbox Identity Store Enabled SSL (else do not select this checkbox). I used connection to be non-ssl (LDAP)
d) Identity Store Server Type : Select from OVD or OID as Identity Store. OVD is optional (use OVD if you have multiple Identity Stores), I used OID (no OVD) as Identity Store. For OVD use case and how to configure OVD for split profile is covered in Oracle Fusion Applications A-Team blog .
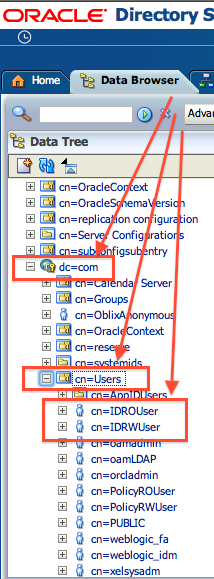
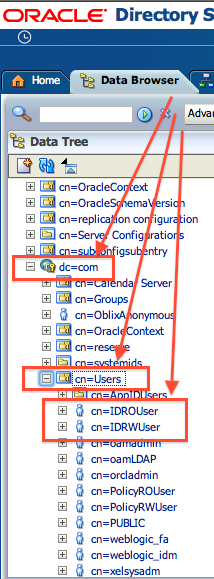
e) Identity Store User DN : cn=IDRWUser, cn=User, dc=com
Note: Change dc=com to your OID Realm (set during OID configuration). To verify your OID realm, login to ODSM and search for user IDRWUser
f) Identity Store Password : Provide password set during this user creation.
g) Identity Store Read-On User DN : cn=IDROUser, cn=User, dc=com
Note: Change dc=com to your OID Realm (set during OID configuration). To verify your OID realm, login to ODSM and search for user IDROUser
h) Identity Store Read-Only Password : Provide password set during this user creation.
Above two users (IDROUser & IDRWUser) are created during idmConfigTool.sh -preConfigIDStore more on idmConfigTool here
- IDRWUser & IDROUser in OID (via ODSM )
- IDRWUser & IDROUser in OIM
For more on parameters in Identity Management screen during Oracle Fusion Applications installation, stay tuned !!